Government access to people’s telecommunications data presents important rule of law issues for discussion. With rapid developments in technology, the law is always battling to keep up, and the Australian Parliament ordered an inquiry into the legislation which allows law enforcement and intelligence agencies to obtain warrants, and information about people’s use of telecommunications services.
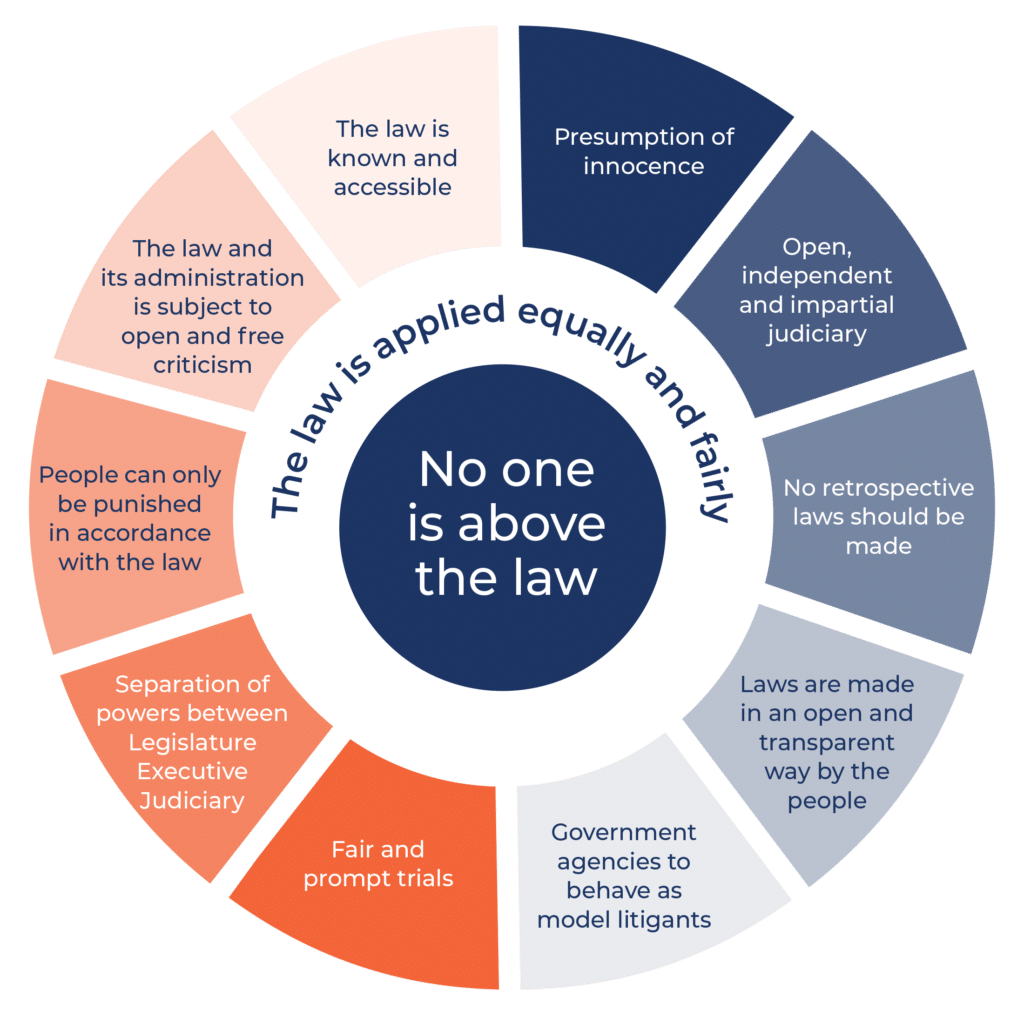
Australia is a respected rule of law country and we want it to remain that way. But whether it does primarily falls onto this parliament to ensure that this country’s laws are simple to understand and not infected by what I might describe as arbitrary discretion.
An arbitrary discretion would be a power granted under law that is too broad or not well defined, so much so that it might be unpredictable, uncertain and be used in a way which does not provide for equality before the law.
An example of an arbitrary discretion would be giving law enforcement agencies the power to search a person, anywhere, anytime, for no reason. The notion that an absolute ruler had the power to pry into any aspect of the lives of any of the ruler’s subjects was emphatically rejected in the The English Bill of Rights, an Act of the Parliament of England which constrained the power of the monarch which prevented the monarch from interfering with the election and work of parliament, and a number of individual rights with prohibitions against issuing cruel and unusual punishments, and other essential protections. This document remains the cornerstone of the rule of law throughout the democratic world. It inspired in part the Bill of Rights and the Fourth Amendment 100 years later in the United States which gave the right of the people to be secure in their homes and houses against unreasonable searches and seizures except by warrant on probable cause.
Public Confidence in the Legal System
The serious problem this parliament has with the Telecommunications (Intercept and Access) Act 1979 is the law being referred to here. It was originally introduced in 1979 and has stood the test of time well considering the huge technological changes which have occurred since the late 1970s.
Telecommunications intercept laws as I see it is there is either little or no public confidence in the system.
It is not just me saying that; a number of respected commentators in this area and professors in universities have said it, including during the last four months. There are several reasons for this if I might address them. Firstly, recordings of Australian telephone calls, emails, SMS, internet records, metadata, voicemails et cetera can potentially be accessed without the person who is the subject of access ever finding out that this has occurred. This is very, very different to what I might describe as a normal search warrant of premises where the occupier is present. The occupier can if he or she thinks their rights have been violated by the search warrant bring proceedings to invalidate the warrant; not so in the case of accessing telecommunications data. That in itself is sufficient, in my view, for parliament to recognise the important need for public confidence in a system that invades their privacy without their knowing and where there can be no right of redress.
However, layered on top of this issue are the many revelations of Edward Snowden we have heard recently and in particular terms we have come to know such as Prism and Tempora, together with the realisation that at least potentially many aspects of the lives of Australians are available to be accessed in one way or another. Metadata by itself can be a rich source of information about a person’s life and their associates.
In making the above comments, I am not suggesting that public confidence be restored by removing any of the various types of interception warrants or stored communications warrants or access to existing or prospective telecommunications data. But, if you are of the view that public confidence has been eroded and you need to restore it, then, in my view, there is a relatively simple solution. When I look at the act, the thing that concerns me the most is the power and the way it is given to the issuing authority that authorises access to telecommunications data generally—and in that I include intercepts.
Problems with the Telecommunications (Interception and Access) Act 1979
Can I outline some of the problems as I see them. Firstly, it is not clear from the Telecommunications (Interception and Access) Act annual report that any telecommunication intercept warrants—and these are the most intrusive types of warrants—ever get refused, because the statistics we have linked together in the one category, refused applications, were withdrawn. So there was a possibility that none of these types of very intrusive interception warrants were refused in the 2013 financial year. Even putting that problem to one side for a moment, we do know from the statistics when we add up the refusals with the withdrawn applications that less than one per cent of applications for service warrants, less than one per cent of applications for named person warrants and less than one per cent of applications for B-party warrants were refused. In the case of warrants authorising the entry onto premises, none were refused.
There are three reasons, I think, for the very low level of refusals—and the difficulty here and the reason public confidence is being eroded is very simple: this process is seen as just a rubber stamp.
The obvious reason for the low level of refusals, and you have probably heard this before, is that the issuing authority only hears from the agency applying for the warrant. It is an entirely one-sided process.
If a warrant is issued when it should not have been, in most cases the person who had their private and confidential communications accessed will never know that this has occurred. This significant imbalance can be rectified by increasing the power given to the issuing authority to rigorously consider and, if appropriate, reject the applications. Unfortunately, this part of the act—I am referring now to chapter 2 and section 46 and I will go to an example—is not about refusing or rejecting applications; it is all about granting them. The usual type of wording you see in search warrants and, indeed, in some parts of the act, though they are in the minority, is as follows—and I take you to section 46, subparagraph (3):
The Judge or nominated AAT member must not issue a warrant in a case in which subparagraph (1)(d)(ii) applies— which is the B-party warrant— unless he or she is satisfied that … You must not issue a warrant unless you are satisfied of the following—that is the standard type of wording we see in search warrants.
However, if you go to section 46, which deals with service warrants, you will not see those words. And it is not just a matter of words. In that, it says, ‘If a member is satisfied of the following things, the judge or AAT member may, in his or her discretion, grant a warrant.’ It is a significant difference in wording, particularly to lawyers. If you want rigorous consideration of these applications, these provisions need to be altered to give the relevant issuing authority the power to say, ‘No, I’m not going to issue this because it does not meet one or more of these criteria.’ Can I also talk in this context about the restrictions and conditions that are placed on search warrants. Surprisingly, there is no express power in chapter 2 that permits the issuing authority to impose conditions or restrictions when an interception warrant is granted. Rather, in a section that talks about the form of the warrant, section 49(2), it simply says:
A warrant may specify conditions or restrictions relating to interceptions under the warrant.
That is a very backhanded approach to what I think should be an express power given to the issuing authority to impose whatever conditions it thinks appropriate, and I think that list should also come with possible examples. When we look at the statistics, which are reported in this annual report, showing where conditions are imposed, for an interception warrant, 2.6 per cent of those contained restrictions or conditions. For a named person warrant, 1.4 per cent had conditions attached. For a B-party warrant, I am pleased to say that it increased to five per cent having conditions attached. In my respectful view, these provisions need to be reworked to make this a more rigorous process. The next thing I wanted to come to is: exactly who is the issuing authority? At present, if we are talking about interception warrants, both AAT members and various judges have been granted the authority to issue interception warrants. In my view, consideration should be given to ensuring that, the more intrusive the warrant, the more senior the judicial officer or AAT member that determines the warrant’s application should be.
I can see no practical reason why the issuing of interception warrants should not be considered only by a Federal Court judge.
Stored Communications
I move now to stored communications, but I really want to make the same point about stored communications. There are relatively few warrants issued. There were 563 issued last year. However, more and more individuals and companies are now storing their confidential and private data in the cloud. Such warrants also seek access to communications, including those in the form of SMSes, emails and attachments to emails. For these reasons, consideration should also be given to having applications for this type of warrant rigorously determined by a Federal Court judge. As stored communication warrants also include telecommunications, the same rigorous consideration that I suggested for telecommunication warrants should be considered. This will, hopefully, ensure proper scrutiny of these types of applications.
Telecommunications Authorisations (Metadata)
The third category is telecommunications authorisations. These authorisations, I am happy to say, are important to law enforcement agency investigations. There is a significant distinction, legally and practically, between the content of a communication and the details of the communication in terms of its metadata. Nevertheless, a lot of personal and confidential information can be inferred from metadata, and examples abound. Being involved in criminal matters as I am, where two defendants might be accused of something, seeing an increase in the communication between them—without knowing what that communication is—at the time of the alleged offence will obviously be of interest to law enforcement agencies. That said, in cases of innocence, you can also tell from that type of material a lot about what that person might have done and the various associates they have. My suggestion is that this process, under chapter 4 of the act, also be reviewed to make it more rigorous—with a view not to reducing the number of applications but only to ensuring proper scrutiny of these applications. There were close to 320,000 applications last year, and there is no suggestion or record in the annual report that any of those were refused or that any conditions were imposed.
What should happen when a warrant is issued that should not have been?
I will deal now with the final two matters I want to deal with, and I will be quite brief. What happens when something goes wrong, and it does—if a warrant was issued that should not have been? We know with warrants in other situations some things can go wrong, and I am referring in particular to the recent matter looked at by the court where the AFP obtained a warrant to search the premises of Channel 7. It is a very different circumstance to what we are talking about here. Nevertheless, things do go wrong. The oversight by the parliament and the ombudsman is important but, I would add, not as important as ensuring that the issuing authority is armed with the necessary legislative tools.
However, if the subject of a warrant or authorisation finds out that information about his activities or communications has been accessed, and that might be in circumstances where he is the defendant in criminal proceedings, that person should be given the express right under the act to challenge the issuing of the authorisation or warrant.
We know from recent experience that an issuing authority can be misled into granting an application for a warrant. I am not suggesting this was done deliberately, but we would be quite wrong to think that that does not occur or that it is unlikely.
In 2002, the United States Foreign Intelligence Surveillance Court released an opinion stating that, in over 75 applications for warrants and wiretaps, the court had been misled by the FBI and the Department of Justice, no less, on those 75 occasions. It is important that, when it is shown that a warrant or authorisation should not have been issued, evidence obtained by that warrant or authorisation should not be allowed to be admitted into evidence in any civil or criminal proceedings.
My submission is that, if these changes I have suggested are adopted in one form or another, various issuing authorities will no longer be seen as little or nothing more than rubber stamps. Applying for warrants and authorisations will be a much more rigorous process. That, in turn, should help restore public confidence in this system, and that should be of benefit to all players, including the law enforcement and other agencies that rely on warrants and authorisations to help keep the same public safe from serious criminal and other activities.
The above is the abridged opening statement of the Institute’s Vice-President, Malcolm Stewart, to the Inquiry into the Revision of the Telecommunications (Interception and Access) Act 1979. See the APH Website for the full unmodified copy of the proceedings.
Headings have been added as a guide to the points being made and underlined terms are popups to explain definitions of terms for educational purposes and are not part of the original transcript. See the APH Website for the full unmodified copy of the proceedings and the Inquiry’s Website.